OpenCTI Threat Intel from another Planet?
So I thought I would post what OpenCTI can show us, visually, the correlations and the cool benefits of when you setup your own OpenCTI instance. Just how neat of a platform it is, compared to MISP or Yeti for comparison. It is a real time, dynamically updated, powerful database of knowledge, that the more it ingests, the smarter it gets. In this example I will be sharing a few screenshots of the "Black Basta" Ransomware campaign using Qbot/Qakbot that's all over your news feed the last few days. Threat Intel companies are reporting major uptick in Qakbot, with mass harm on their agenda, and these guys are a large part of the reason for it.
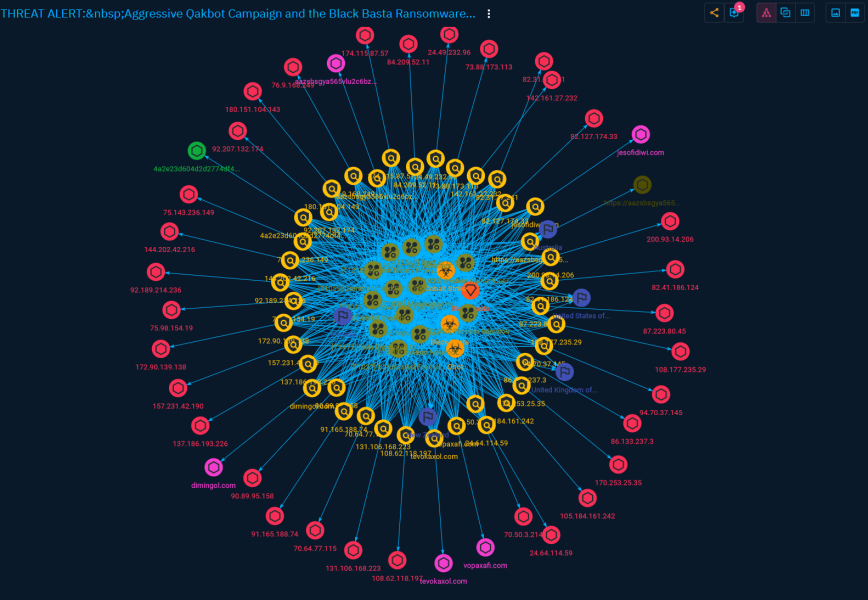
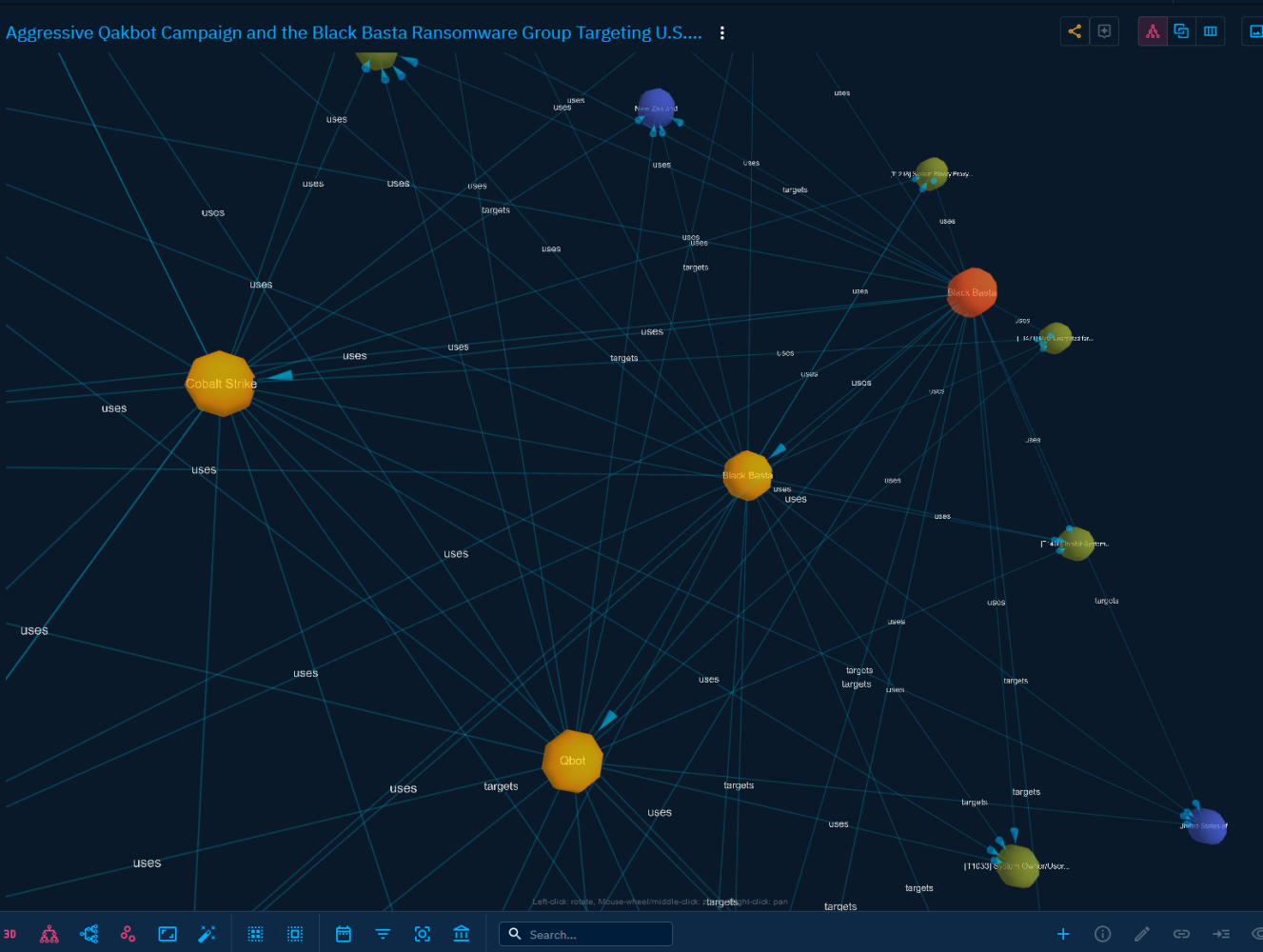
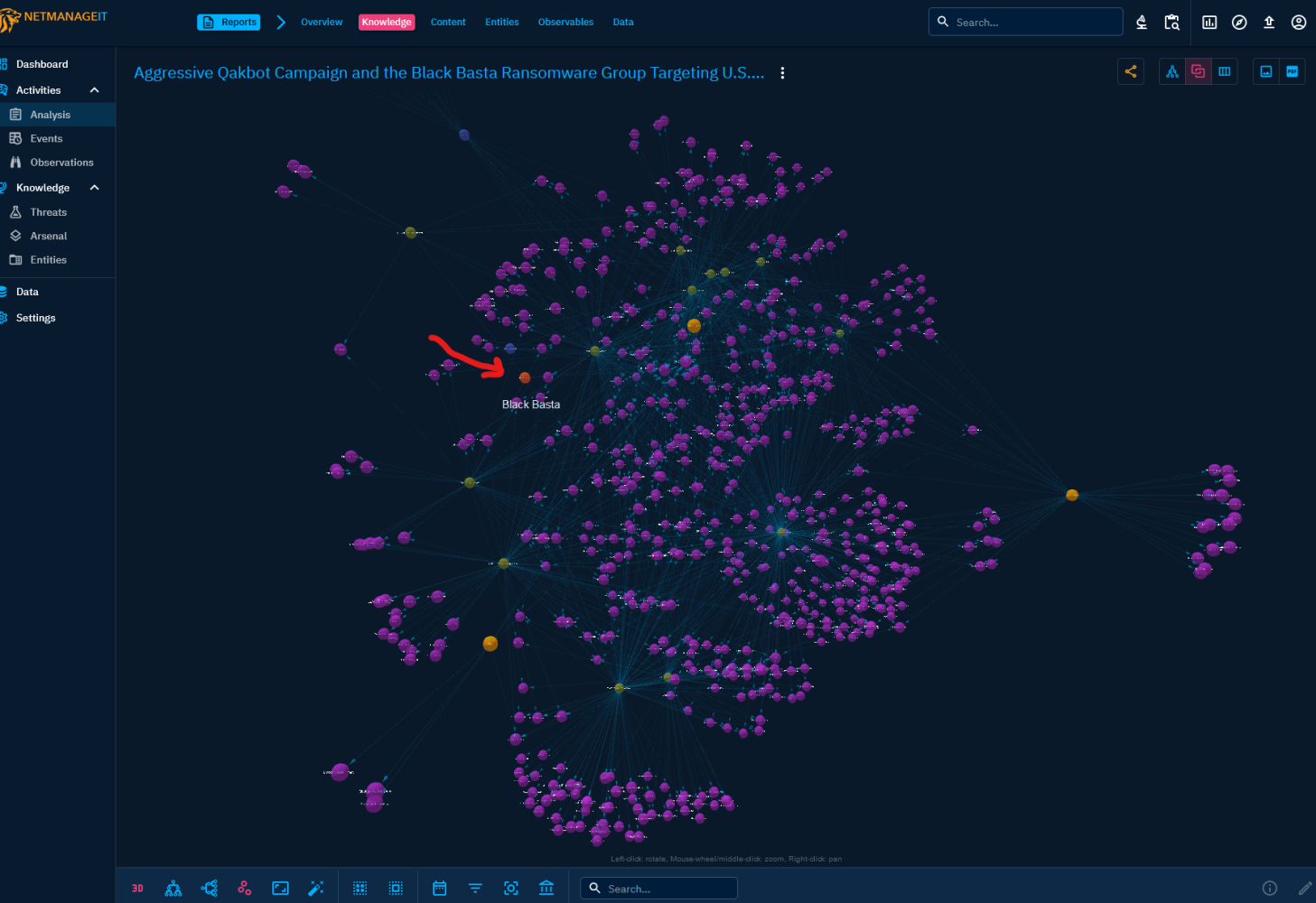
You may be like, "why do these visualization look like DNA, or Cell's, or Planets in space?" :) Well depending on the view, it is attempting to visualize key parts of the campaign, the attacks used, who is attacked, the MITRE techniques, indicators and observables, and joining them all together in a 3D or 2D map for you to get a visual representation of how things are interconnected, where things originate from, things in common etc.
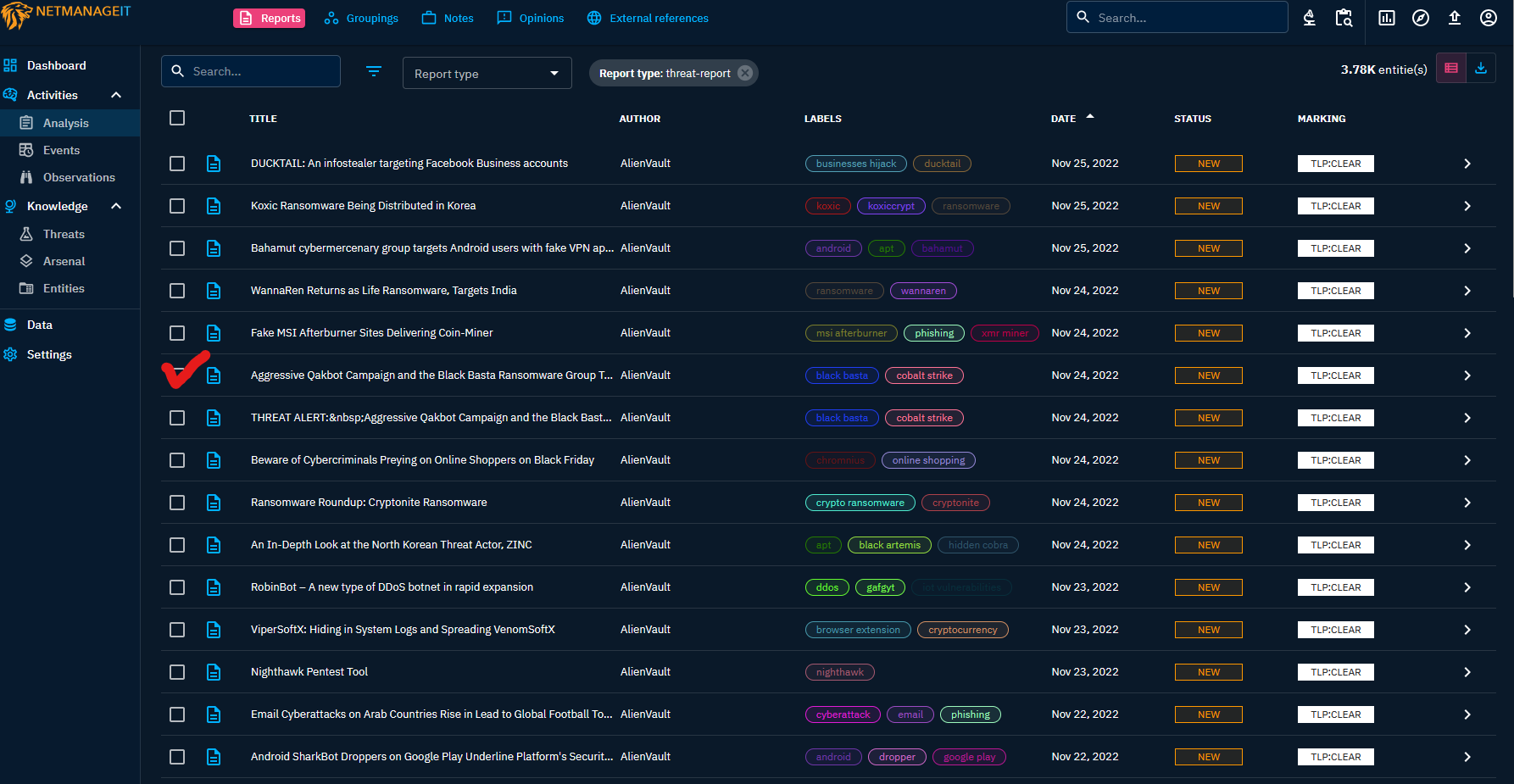
In this 1st view, you see Reports hot off the wire, updated from your favorite connectors and the tags OpenCTI enriches and labels the data with. The system, like Elasticsearch for example, is meant to visualize and sort through massive amounts of data, and allow powerful searching and correlation, so you can find that needle in a haystack, that otherwise would be harder to hunt for, do research on etc.
I am going to select the Report indicated by the check mark and we can start to drill into this Intel.
In the second view, you can see a summary about the bad guys campaign of dastardly deeds. :) Notice the two check marks, these are external URL references with 3rd party detailed "coverage / knowledge" of its inner workings, think of it as a Intelligence briefing.
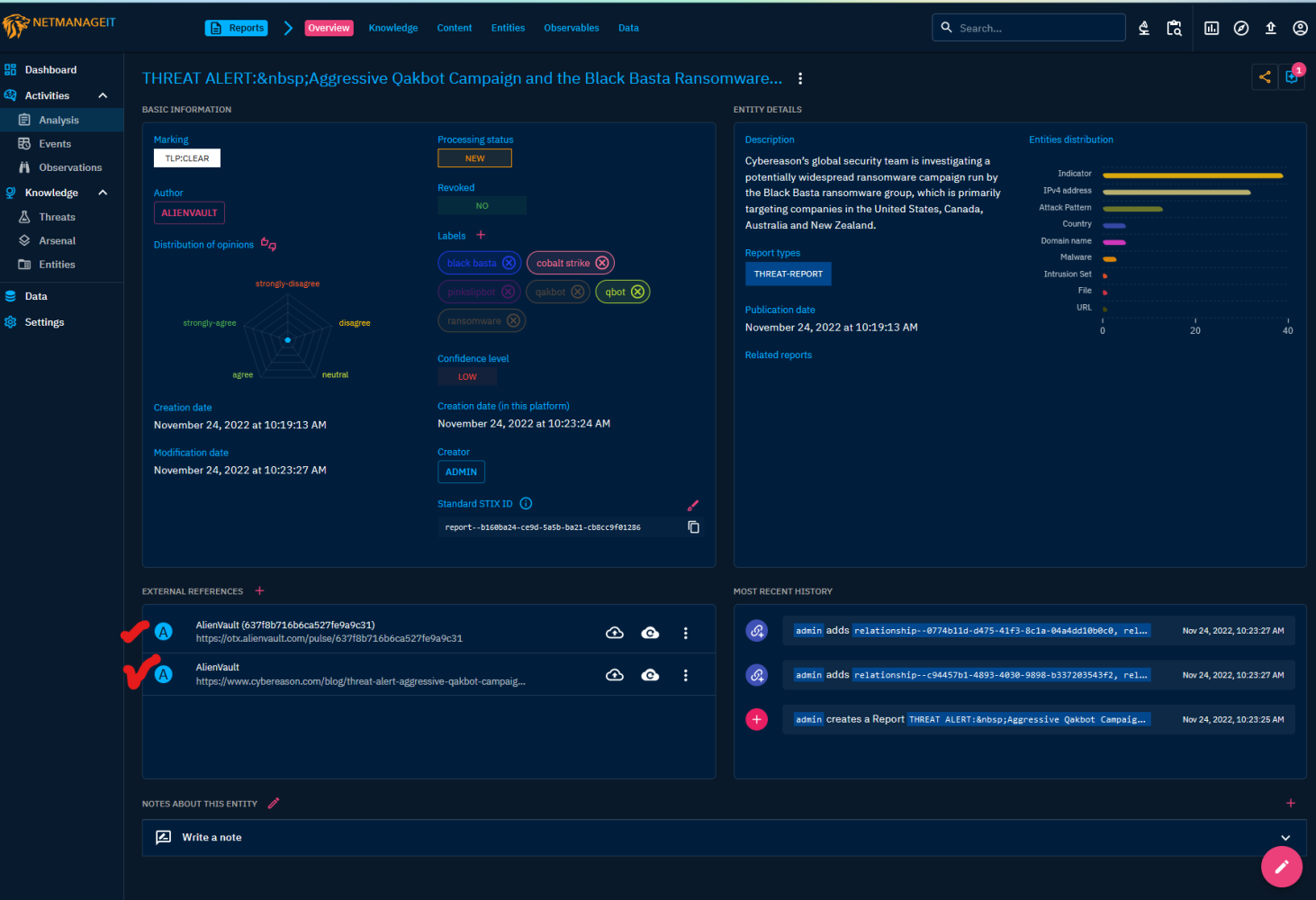
Clicking one of the two links takes you two one of two sites.
CyberReason's report : https://www.cybereason.com/blog/threat-alert-aggressive-qakbot-campaign-and-the-black-basta-ransomware-group-targeting-u.s.-companies
AlienVault's report/OTX Pulse: https://otx.alienvault.com/pulse/637f8b716b6ca527fe9a9c31
AlienVault link screenshot:
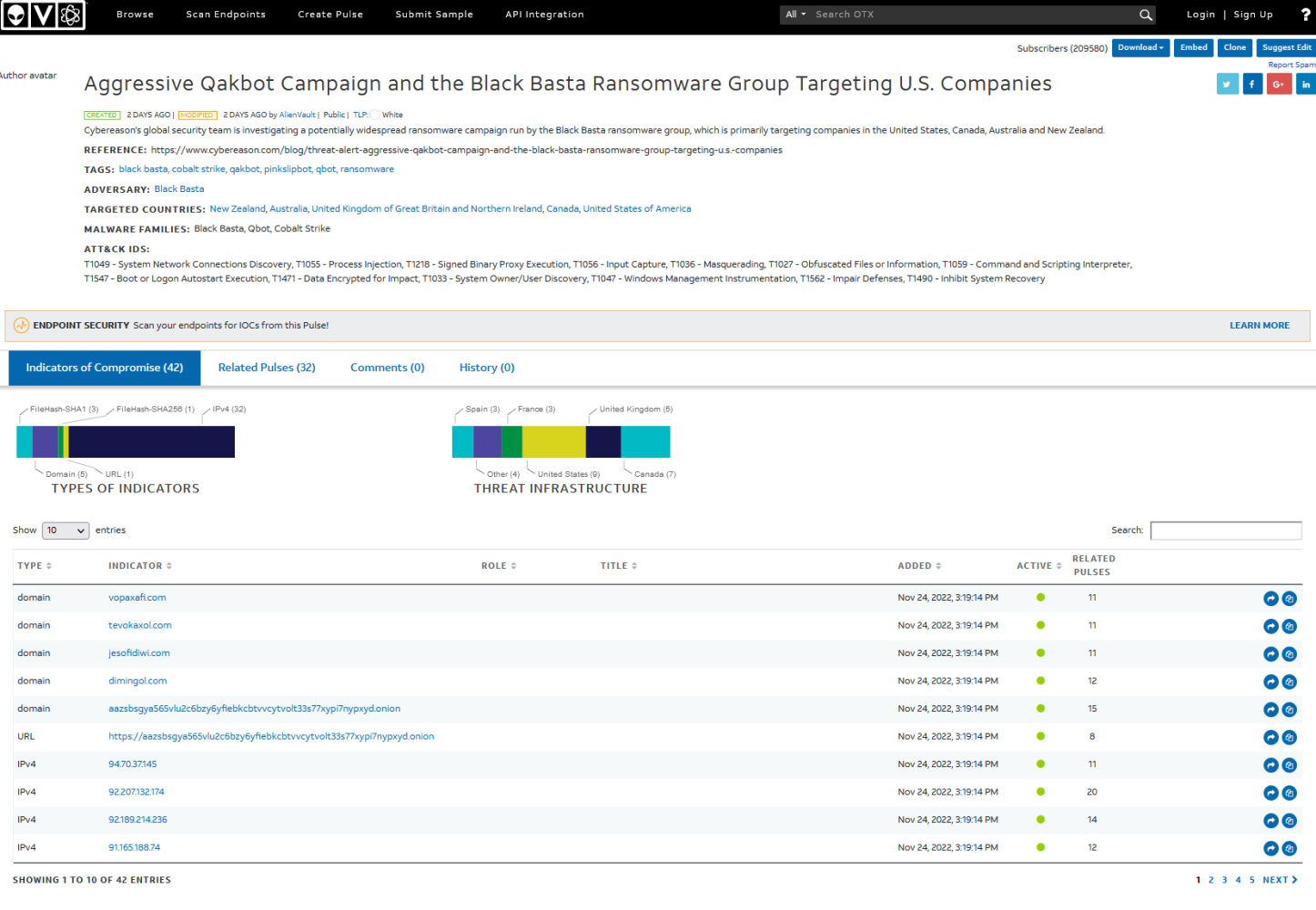
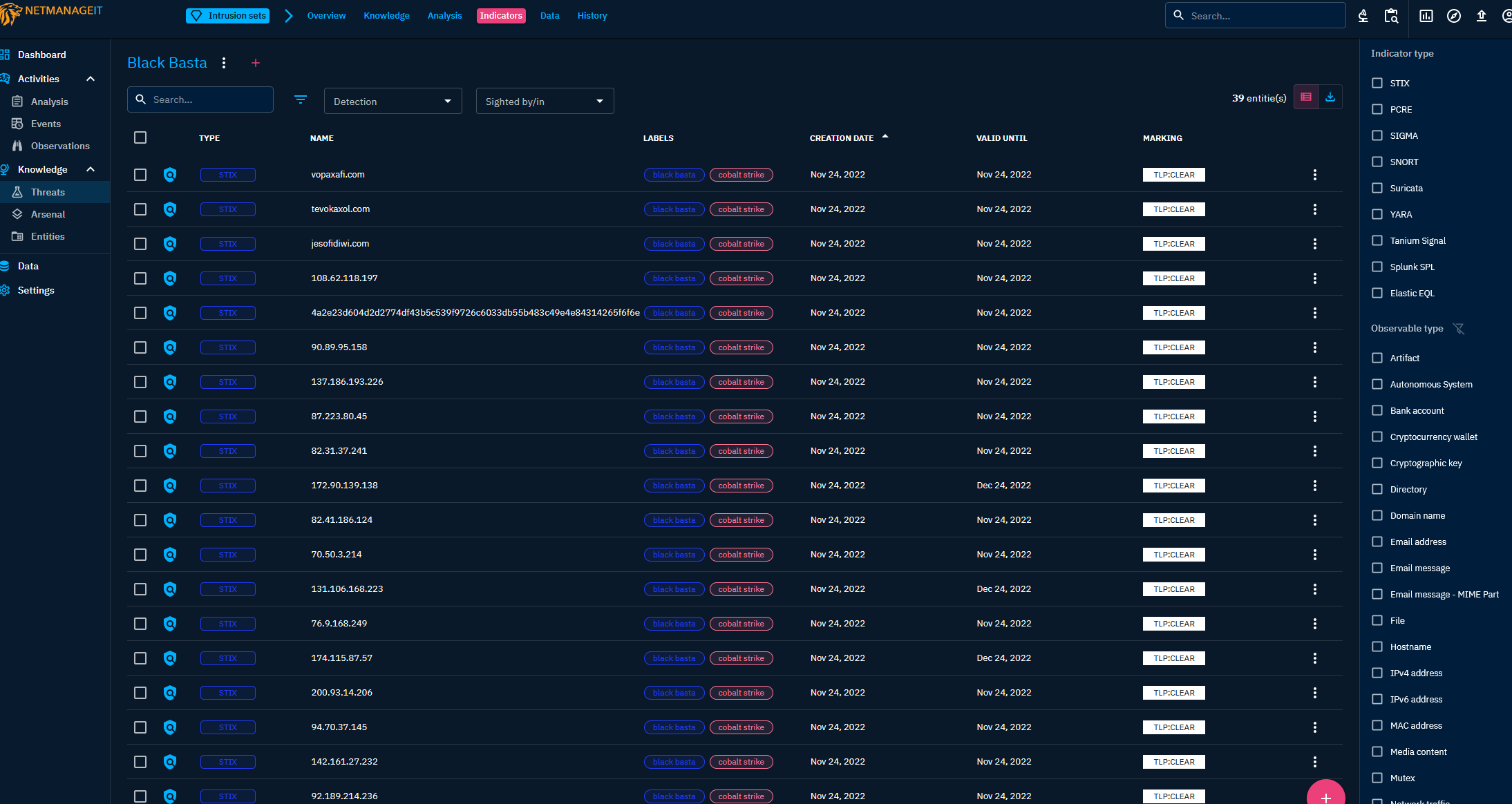
By clicking some additional options on the row up top of OpenCTI, you access more details such as Indicators, domain names, IP address's in use by this campaign. Useful for adding to a blocklist, or cross referencing (correlating) to see past malicious behavior by this IP/Domain in the past for example. That is where OpenCTI shows its strength, it enriches all the past data, with new data, correlates, and links item's from one threat to another, so you can see commonalities between the data, overall trends etc. You also have full search capabilities from anywhere in the UI. Even full search for a questionable IP/domain via API to and from other platforms.
Here we see Indicators by selecting the indicators tab:
Now whats really really neat, dare I use the word "CyberThreatPorn", is the Analysis tab, where you can show 3D rotatable visualizations to show all the correlations in this campaign, and with everything else currently ingested into your OpenCTI platform. Going back to it looking like a galaxy, or interconnected DNA, there is some similarities between these actually. :)
1st view simple campaign only visualization.
Now a zoomed out correlation where the Black Basta, Qbot, tactics and indicators are all interconnected with all the other data in the OpenCTI platform. You can spin this around, zoom in and out, and move it around like a 3D model if you will.
It's starting to look like a "YOU ARE HERE" picture from Hitchhikers Guide to the Galaxy. Black Basta small Orange sphere indicated by red arrow.
If you spin up your own OpenCTI instance, follow the prior guide I wrote. You will learn so much, I can't think of a better learning tool for those starting off in the Cyber field, or even for those seasoned veterans! I will leave you with a famous Hitchhiker's quote.
Nothing travels faster than the speed of light with the possible exception of bad news, which obeys its own special laws.”
There can be a lot of bad news with so much malice taking place out there, get ahead by getting the data straight from the source's real time, rather than wait for some other person or company to do a write-up on the latest threats!


