ASN OSINT Trace Route tool on Steroids

After writing the 60 Hudson Street article, I stumbled across this awesome command line tool to do OSINT on network path traversal. Some of the capabilities of this tool are ASN / RPKI validity / BGP stats / IPv4v6 / Prefix / ASPath / Organization / IP reputation / IP geolocation / IP fingerprinting / Network recon / lookup tool / Internet trace route server and Shodan lookups.
If you wanted to find the ASN info and Peering information of all the hops in your packets network path from source to destination, this tool is awesome! There really isn't an official name of the tool, but here is the Github repository for the tool is below.
I won't include all the capabilities in the tool, but will give a few examples with screenshots. Full description and use of each function can be read at the link above. Lets do a few commands to get it installed, I am using Ubuntu 22.04 on my workstation, the different distro instructions differ slightly and are referenced on Git.
Installation:
apt -y install curl whois bind9-host mtr-tiny jq ipcalc grepcidr nmap ncat aha
Then run the install script:
curl "https://raw.githubusercontent.com/nitefood/asn/master/asn" > /usr/bin/asn && chmod 0755 /usr/bin/asn
Now to show a few examples of what it can do.
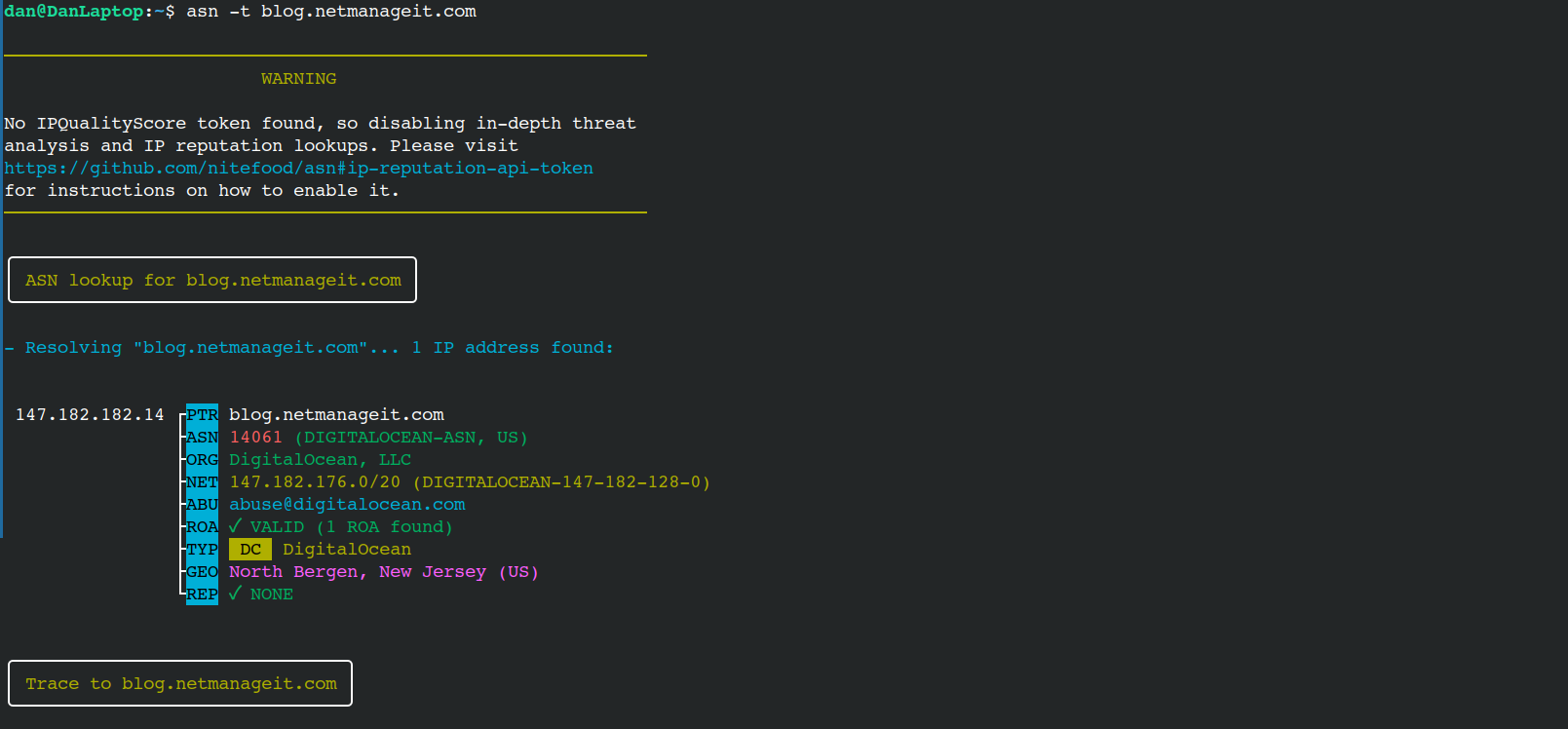
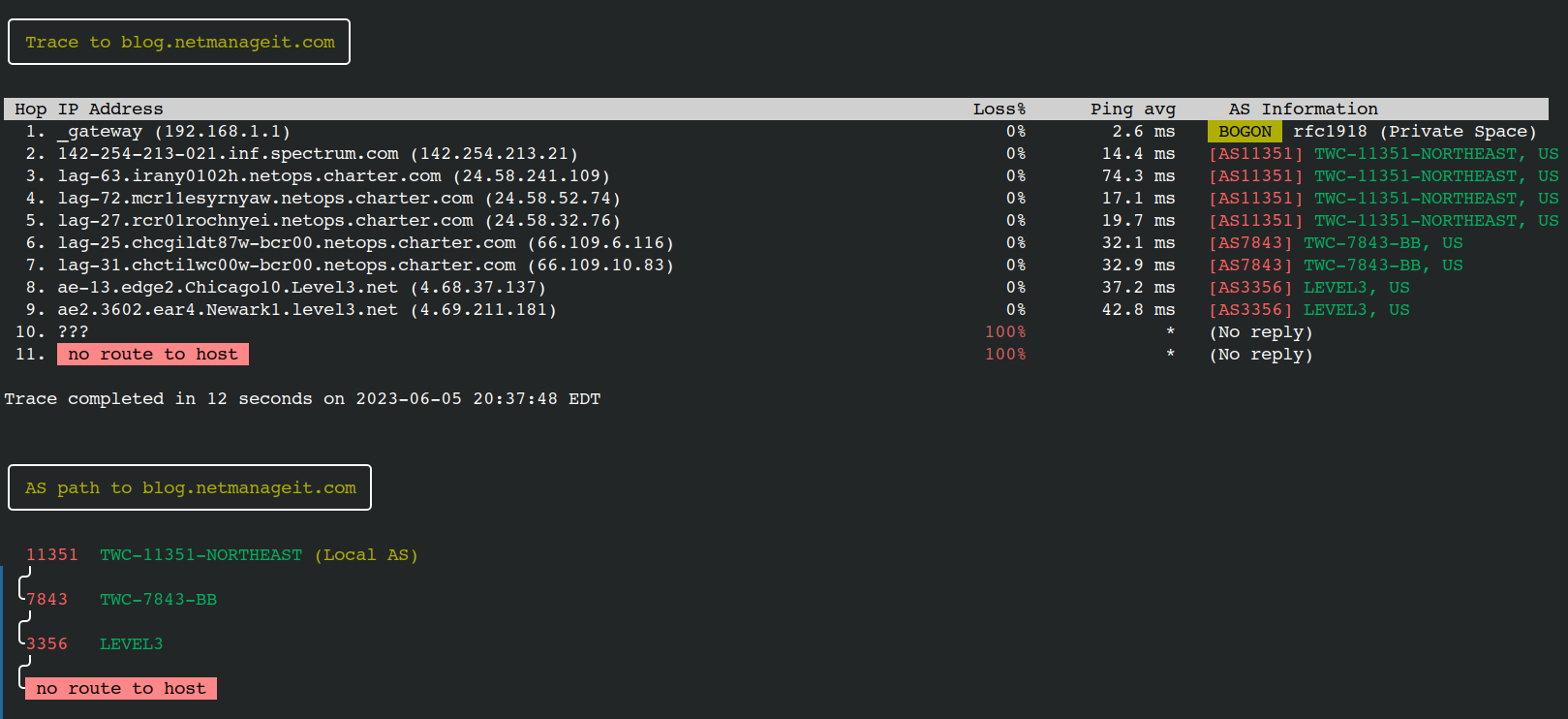
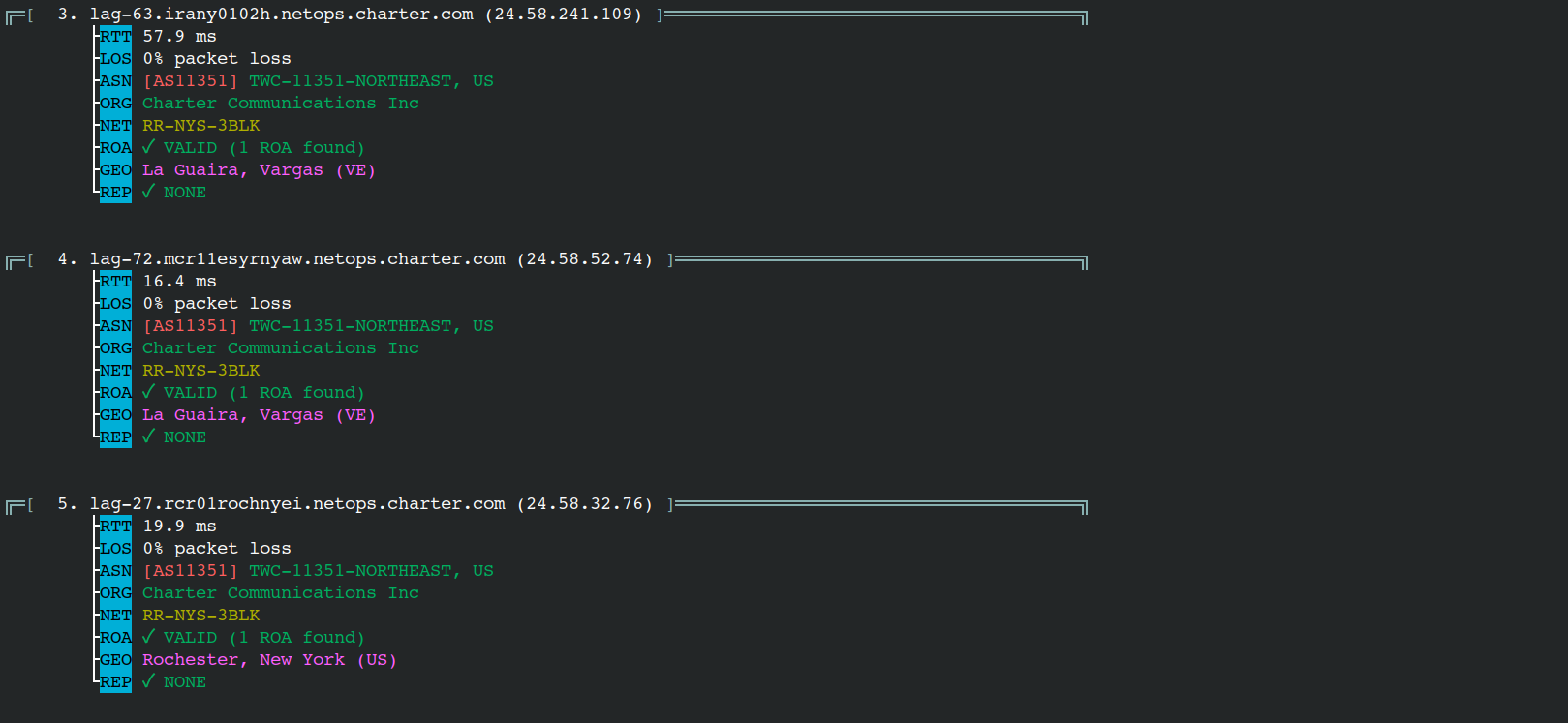
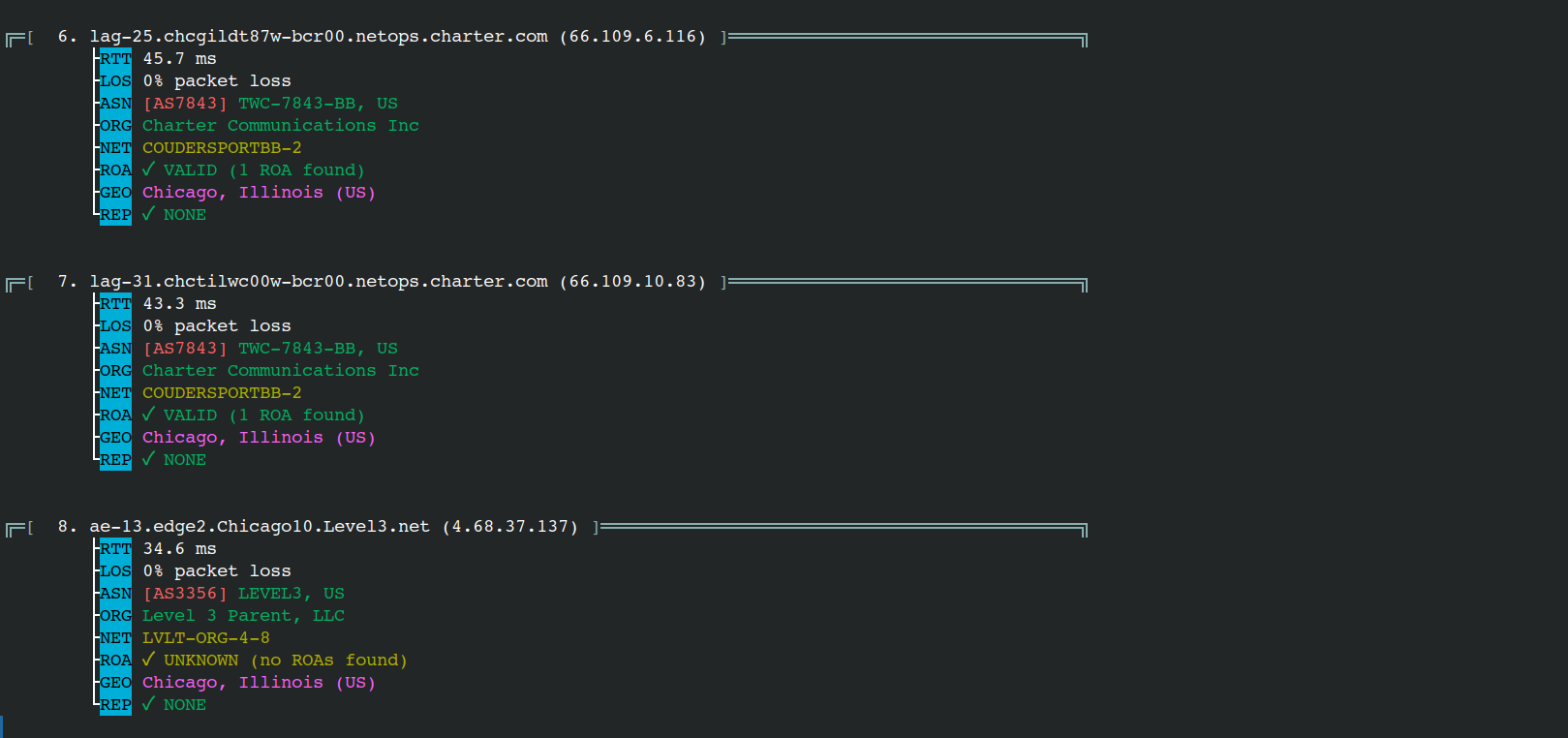
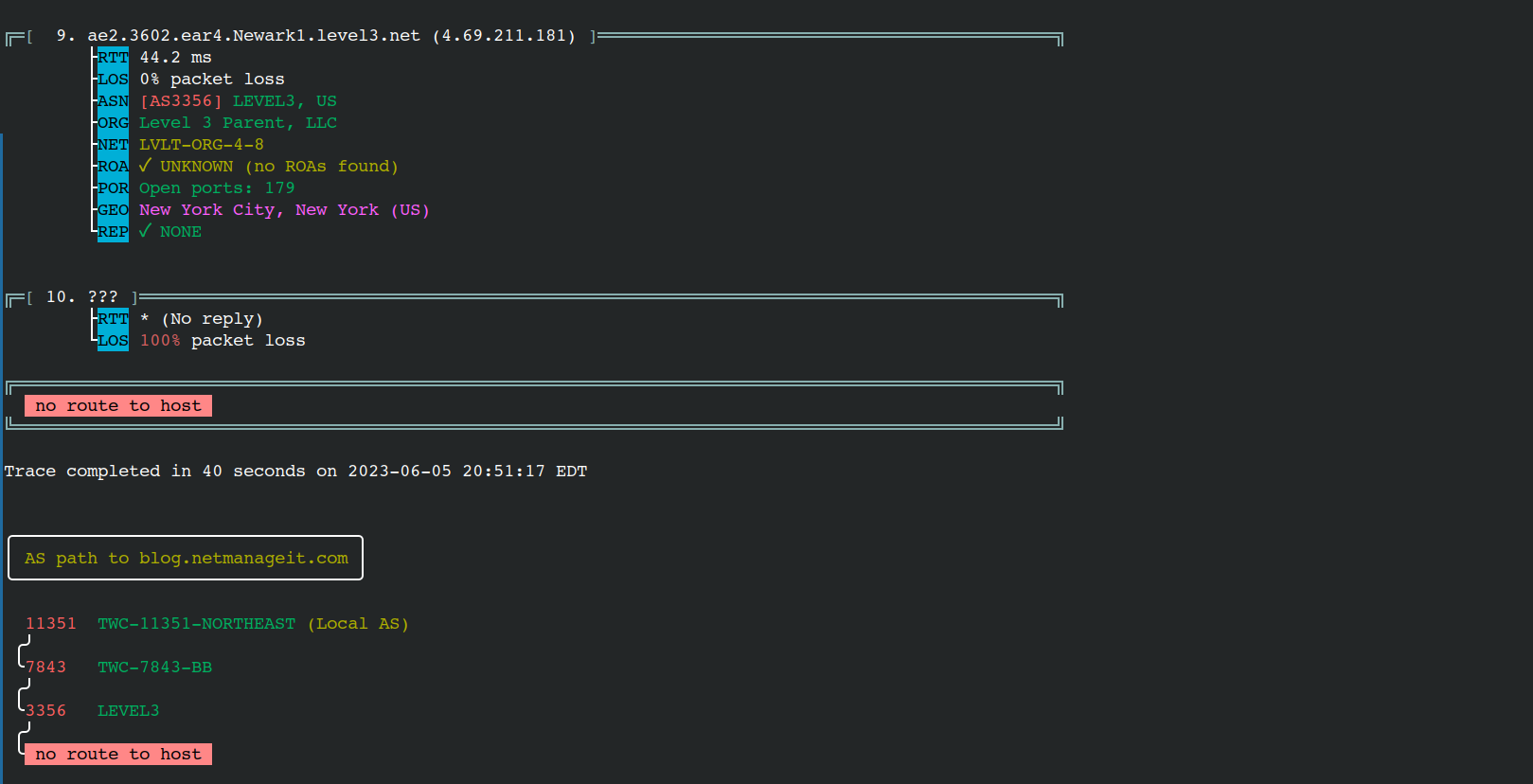
Let's first try a Lookup and Network path trace using a " -t " option
asn -t blog.netmanageit.com
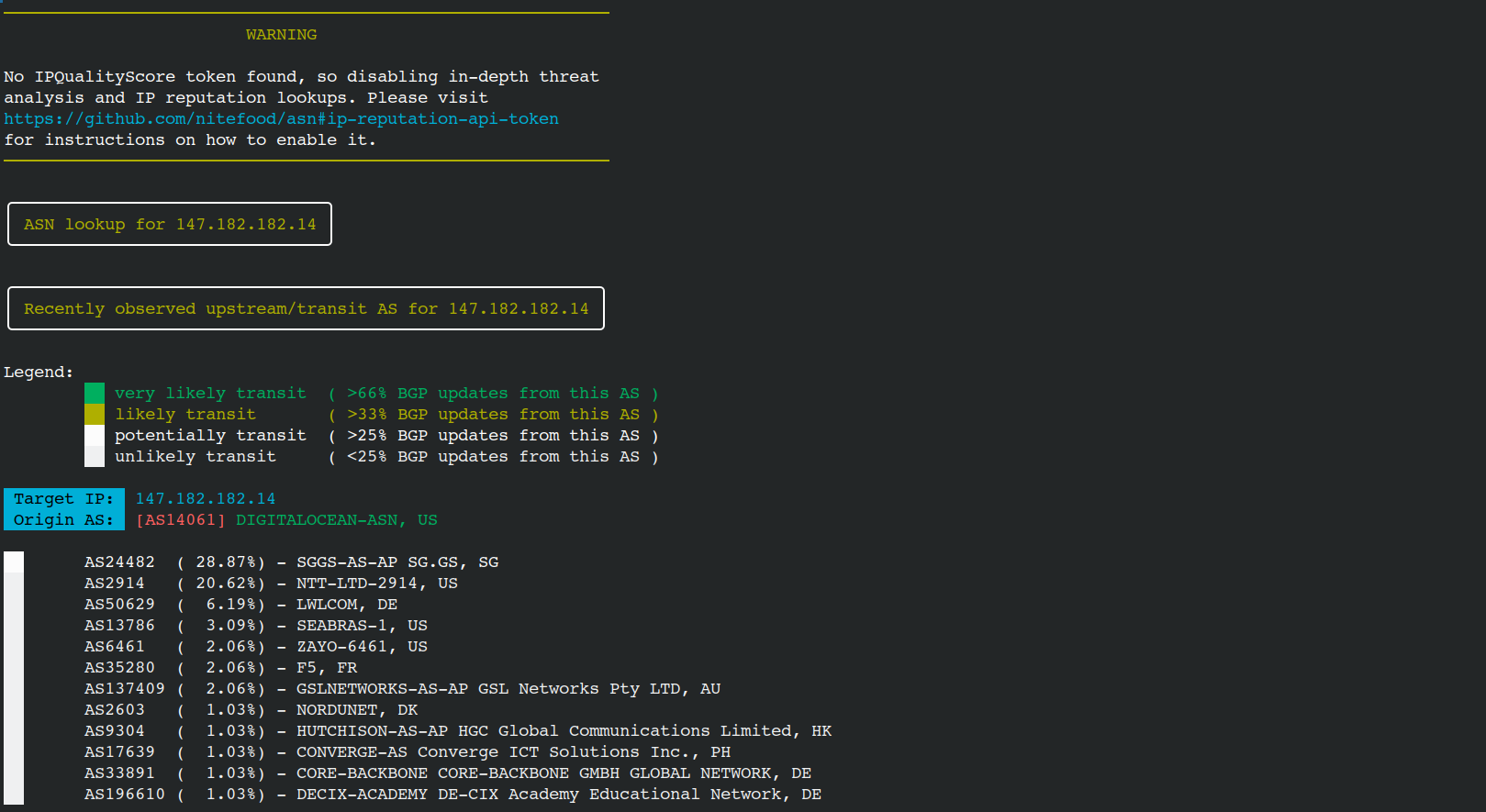
Next lets try a "Transit/Upstream Lookup" using the " -u " option. This will inspect BGP updates and ASPATHs for the TARGET address/prefix and identify possible transit/upstream autonomous systems.
Note: This option requires an IP Address.
asn -u 147.182.182.14
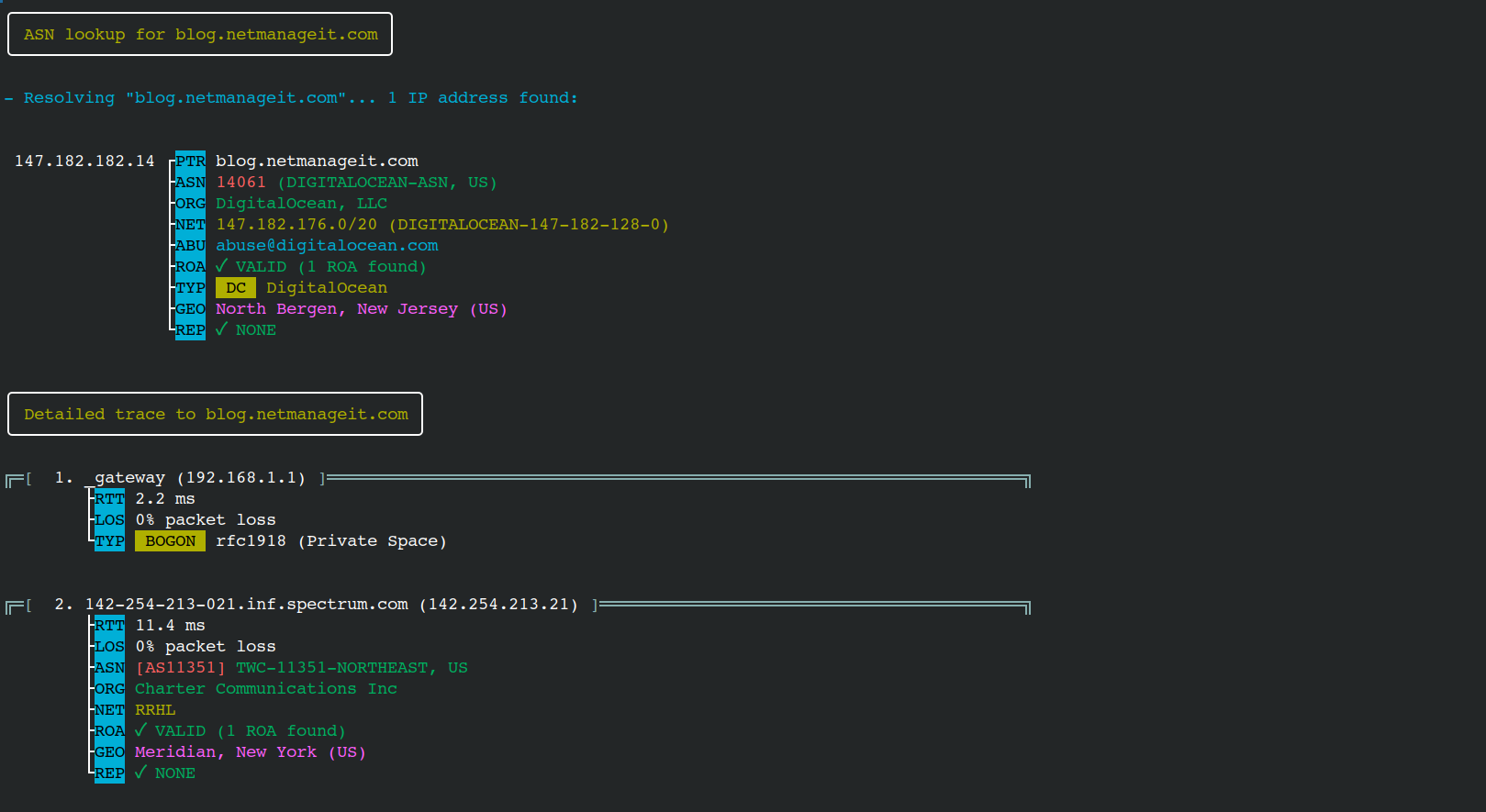
Finally lets do a Detailed Trace using the " -d " option.
asn -d 147.182.182.14
Some other very useful commands are " -s " for Shodan , " -g " for Geolocation mode, and finally " -l " to spin up a simple web server to use as an interface!
I hope you find this very useful network tool as handy as I have.
Till Next time
Dan



